Starting from Windows Server 2012, Microsoft added a feature in Failover Cluster, Cluster-Aware Updating (CAU). Cluster-Aware Updating (CAU) is a feature for applying Windows updates to a cluster that includes all nodes. Cluster-Aware Updating (CAU) can also import a plug-in and then install drivers or firmware to a cluster.
Cluster-Aware Updating (CAU) will instruct clusters to the following steps to apply updates.
- All cluster nodes download updates from the source
- Put one of cluster nodes to maintenance mode
- Move all related cluster roles from the cluster nodes which will install updates to other cluster nodes
- Install updates to the cluster node which is in maintenance mode
- After installing the update, the server may need to restart
- After restart, the cluster node join the cluster and exit maintenance mode
- Repeat the above steps for other cluster nodes
Cluster-Aware Updating (CAU) apply updates to one of cluster nodes each. Cluster-Aware Updating (CAU) is a cluster scope based feature. You cannot apply updates to a specific nodes by Cluster-Aware Updating (CAU).
There are 2 modes of Cluster-Aware Updating (CAU) which are "Self-updating mode" and "Remote-updating mode". "Self-updating mode" is a mode for clusters to configure the update schedule and then follow the schedule to install updates by themselves. "Remote-updating mode" is a mode to control the clusters to apply updates from a remote computer. Before using both modes of Cluster-Aware Updating (CAU), administrators need to configure the following prerequisites
Enable Windows Management Instrumentation
By default, all Windows Servers have been enabled Windows Management Instrumentation (WMI) in Windows Server 2012 or Windows Server 2012 R2.
If not, click to enable it on Server Manager.
Or perform "Set-WsManQuickConfig" as administrator in a PowerShell console to enable it.
Enable Windows PowerShell and Windows PowerShell remoting
By default, all Windows Servers have been enabled PowerShell remoting in Windows Server 2012 or Windows Server 2012 R2.
If not, perform "Enable-PSRemoting" as administrator in a PowerShell console to enable it.
Install .NET Framework 4.5
By default, all Windows Server 2012 or Windows Server 2012 R2 have been installed Microsoft .NET Framework 4.5.
If not, launch "Server Manager > Add Roles and Features" to install Microsoft .NET Framework 4.5
Or perform "Install-WindowsFeature NET-Framework-45-Core, NET-WCF-TCP-PortSharing45" as administrator to install the feature.
Enable a firewall rule to allow automatic restarts
We need to configure the Windows Firewall rules in cluster nodes to allow the inbound TCP protocol to remote shutdown. To update the firewall rules, we can apply it by "Group Policy" or update it from GUI or PowerShell on each node.
GUI
1. Launch "Windows Firewall with Advanced Security" in a cluster node.
2. Right-click "Inbound Rules > New Rule".
3. On "Rule Type" window, select "Predefined > Remote Shutdown".
4. Click "Next".
5. On "Predefined Rules" window, check all rules.
6. Click "Next".
7. On "Action" window, select "Allow the connection".
8. Click "Finish".
9. Right-click "Inbound Rule for Remote Shutdown (RPC-EP-In)", select "Properties".
10. Select "Advanced" tab.
11. Next to "Profiles", check "Domain" only.
12. Click "OK".
13. Repeat step 9 -12 for "Inbound Rule for Remote Shutdown (TCP-In)".
PowerShell
Launch "PowerShell" as administrator and then perform "Set-NetFirewallRule -Group "@firewallapi.dll,-36751" -Profile Domain -Enabled True -PassThru" to enable the firewall rule in a cluster node.
Remark: You will discover the following error If "Inbound Rule for Remote Shutdown (RPC-EP-In)" and "Inbound Rule for Remote Shutdown (TCP-In)" are deleted.
Administrators need to perform "New-NetFirewallRule -DisplayName "Inbound Rule for Remote Shutdown (RPC-EP-In)" -Group "@firewallapi.dll,-36751" -Profile Domain" and "New-NetFirewallRule -DisplayName "Inbound Rule for Remote Shutdown (TCP-In)" -Group "@firewallapi.dll,-36751" -Profile Domain" to create and enable the firewall rules.
Change the "Windows Update settings" to "Never check for updates"
Microsoft suggested that the "Windows Update settings" should be changed to "Never check for updated (not recommended)" in all cluster nodes which will be used Cluster-Aware Updating (CAU) because there is a own update schedule for Cluster-Aware Updating (CAU) itself.
Make sure all cluster nodes download updates from the same update source like a WSUS server.
If you use Group Policy to apply the "Windows Update settings", you should select "2 - Notify for download and notify for install".
Goal
- Testing "Self-updating mode" in a cluster named CU01
- Testing "Remote-updating mode" in a cluster named CU01
Lab environment
- All servers are installed Windows Server 2012 R2 Datacenter version
- DC01 is a domain controller of test.tls1.lab
- All cluster nodes have been joined test.tls1.lab
- There are 7 cluster nodes with node majority quorum joined a cluster, CU01
- The cluster nodes named, CS01, CS02, CS03, CS05, CS06, CS07, CS08
- Windows Server Update Services is installed in a server named CS04
- All cluster nodes pointed to CS04 to download updates (Optional)
Lab
To simplify the steps, I will use domain administrator to complete the lab.
Testing "Self-updating mode"
1. On CS01, log in as Domain Administrator.
2. Launch "Cluster-Aware Updating".
3. On "Cluster-Aware Updating" window, next to "Connect to a failover cluster", enter "CU01" and then click "Connect".
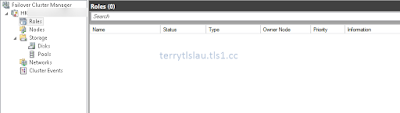
All cluster nodes haven't been updated.
4. Click "Analyze cluster updating readiness".
There are 2 warning in this readiness result. The first one is about machine proxy setting. If the cluster is in a branch office, you may need to configure the proxy settings on cluster nodes. We can ignore it at this moment. The second one is if we use "Self-updating mode", we need to configure CAU clustered role in this cluster. We will configure CAU clustered role.
Remark: We can also perform "Test-CauSetup" on PowerShell console to run the readiness check.
5. Click "Close".
6. Click "Configure cluster self-updating options"
7. On "Getting Started" window, click "Next".
8. On "Add CAU Clustered Role with Self-Updating Enabled" window, check "Add the CAU clustered role, with self-updating mode enabled, to this cluster".
9. Check "I have a prestaged computer object for the CAU clustered role" and then enter "CAU01".
If the cluster is under default container like "Computer", we don't need to prestage a virtual computer object for the CAU clustered role. If not, please create a computer object in Active Directory Users and Computers and then grant "Allow - full control" for "CU01".
After that, disable "CAU01".
10. Click "Next".
11. On "self-updating schedule" window, leave default settings.
We can configure the schedule for this cluster so we don't need to follow the WSUS update schedule.
12. Click "Next".
13. On "Advanced Options" window, there are some options we need to be aware.
StopAfter: Time in minutes after which the Updating Run will be stopped if it has not completed. By default, it is "Unlimited time".
MaxFailedNodes: After applying update to a cluster node, the cluster node may not boot up. We need to determine how many nodes are able to fail in this cluster.
RequireAllNodesOnline: By default, this value isn't checked.
RebootTimeoutMinutes: By default, this value is 15 mins. We may change it for a physical node.
In "Advanced Options", we can also assign pre update script for before installing update and post update script for after installing to a cluster.
14. Leave default settings, click "Next".
15. On "Additional Options" window, check "Give me recommended updates the same way that I receive important updates".
16. Click "Next".
17. On "Confirmation" window, click "Apply".
18. On "Completion" window, click "Close".
Now, the cluster, CU01, follow the schedule to download and install update to all nodes. However, we can apply it immediately by clicking "Apply updates to this cluster".
Now, I will check the current updates for all cluster nodes.
19. Click "Preview updates for this cluster".
20. On "Preview Updates" window, click "Generate Update Preview List".
The current plug-in, "Microsoft.WidnowsUpdatePlugin", is used to connecting Windows Update servers or a Windows Server Update Services (WSUS) server. To install standalone update, we need to additional settings and select "Microsoft.HotfixPlugin".
To install firmware and drivers, we need to import a plug-in from vendors.
There are 3 updates available for all cluster nodes.
Remark: We cannot select or un-select the Windows updates from this window to apply to cluster nodes. To control the Windows updates, Administrators can control it from WSUS server or from "Windows Update" panel.
21. Click "Close".
22. Click "Apply updates to this cluster".
23. On "Getting Started" window, click "Next".
24. On "Confirmation" window, click "Update".
25. On "Completion" window, click "Close".
All cluster nodes are downloading updates from the same source, CS04.
One of cluster nodes, CS05, changed to maintenance mode and started to install the Windows updates.
After installing Windows updates finished, CS05 restart automatically.
When the server boot up successfully, it left maintenance mode.
Make sure Windows updates have been succeeded to apply to a cluster node, Cluster-Aware Updating (CAU) instructs another cluster node to change to maintenance mode and then install Windows update.
As a result, all cluster nodes have been installed Windows updates.
26. Click "Generate report on past Updating Runs".
27. On "CU01 - Generate Updating Run Report" window, click "Generate Report".
We can see which update and installation date of Windows updates were applied.
Testing "Remote-updating mode"
Administrators can install "Failover Cluster Management Tools" and "Failover Cluster Module for Windows PowerShell" features on Windows 8, Windows 8.1, Windows Server 2012 or Windows Server 2012 R2 to manage Cluster-Aware Updating (CAU).
1. To use "Remote-updating mode", launch "Cluster-Aware Updating" on a remote computer as Domain Administrator.
2. Connect to the cluster.
3. Then we can click "Apply updates to this cluster" without configuring "CAU clustered role".
4. On "Getting Started" window, click "Next".
5. On "Advanced Options" window, leave default settings, click "Next".
6. On "Additional Options" window, leave default setting, click "Next".
7. On "Confirmation" window, click "Update".
8. On "Completion" window, click "close".
As a result, Cluster-Aware Updating (CAU) is running in "Remote-updating mode" and work fine.
Remark: We can perform "Invoke-CauRun" to request a cluster to download and install the update.
More information:
This posting is provided “AS IS” with no warranties, and confers no rights!