Local Administrator Password Solutions (LAPS) is a solution provided by Microsoft to manage the local administrator account on domain members which are included workstations and servers. LAPS extended Active Directory Schema to store each password of domain members into an Active Directory attribute, ms-Mcs-AdmPwd. By default, domain administrators can read this attribute to get the password of local administrator accounts but we can configure delegation to allow other groups or users to get it. Using LAPS to manage the password, it can change the password of local administrator account periodically because LAPS is needed to work with Group Policy.
LAPS tool requirement
Lab environment
Prerequisites
Download and save LAPS installation files on C:\Temp of MS01 from the following web site. Local Administrator Password Solution (LAPS)
Make sure the configuration account is a member of Schema Admins of your domain forest.
Install Group Policy Management Console and AD DS and AD LDS Tools on MS01.
Lab
1. Log in MS01 as Domain Administrator.
2. Navigate to C:\Temp and then run LAPS.x64 to install LAPS with full installation.
3. Launch PowerShell as administrator.
4. Perform Import-Module AdmPwd.Ps to import the PowerShell module for LAPS.
5. Perform Update-AdmPwdSchema on PowerShell to extend Active Directory Schema.
ms-MCS-AdmExpirationTime and ms-Mcs-AdmPwd attributes have been added into you Active Directory Schema for computers.
6. Perform Find-AdmPwdExtendedRights -Identity Workstations to check current permission to read these attributes.
7. Perform Set-AdmPwdComputerSelfPermission -Identity Workstations to grant permissions for computer accounts which is under this OU to update the managed local administrator password and expiration date.
8. Perform Set-AdmPwdReadPasswordPermission -OrgUnit Workstations -AllowedPrincipals R1 to great domain user account, R1, to read these attribute.
9. Launch GPMC and the create a new GPO under Workstations OU on MS01.
Remark: The GPO for LAPS is required to create and configure by the Management PC because the GPO template is installed on it only.
10. Edit the GPO and then extend "Computer Configuration > Policies > Administrative Templates > LAPS".
11. Double click Password Settings and then select the following settings.
Password Settings: Enabled
Password Complexity: Large letters + small letters + number + specials
Password Length: 16
Password Age (Days): 30
12. Click OK.
13. Double click Name of administrator account to manage and then select the following settings.
Name of administrator account to manage: Enabled
Administrator account name: <local administrator account name of computers>
Test result
At this moment, W7 and W8 have been installed LAPS. I will install LAPS on W7 to verify the result.
Retrieve Password
1. On W7, log in as Domain Administrator.
2. Run LAPS installation tool with typical installation.
We can create a script to silent install LAPS tool by the following command.
msiexec /i LAPS.x64.msi or LAPS.x86 .msi /quiet
3. After installation, perform gpupdate /force to update the Group Policy.
4. Back to MS01, log in as R1.
5. Launch LAPS UI.
6. Under "ComputerName", enter W7 and then click Search.
The policy is applied to W7 and the password of Nimda on W7 is followed the GPO setting to generate it.
7. Under "ComputerName", enter W8 and then click Search.
The password of Nimda on W8 cannot be retrieved because LAPS hasn't been installed on W8.
8. On MS01, log in as R2.
9. Launch LAPS UI.
10. Under "ComputerName", enter W7 and then click Search.
R2 cannot retrieve the password of W7 because we didn't grant permission to R2.
Remark: We can perform Get-AdmPwdPassword -ComputerName <computername> to get the local administrator password by PowerShell.
Reset Password
1. On MS01, log in as R1.
2. Launch LAPS UI.
3. Under "ComputerName", enter W7 and then click Search.
4. Change "New expiration time" to next day and then click Set.
R1 got the message "Failed to request password reset" because we haven't granted permission to R1 to reset local administrator password of W7.
5. On MS01, log in as Domain Administrator.
6. Launch LAPS UI.
7. Under "ComputerName", enter W7 and then click Search.
8. Change "New expiration time" to next day and then click Set.
The local administrator password of W7 will be reset next day.
9. To grant R1 to reset local administrator password, we can perform Set-AdmPwdResetPasswordPermission -OrgUnit Workstations -AllowedPrincipals R1
Remark: We can perform Rest-AdmPwdPassword -ComputerName <computername> -WhenEffective <Date & Time> to reset the local administrator password by PowerShell.
More information:
Microsoft Security Advisory 3062591
Local Administrator Password Management Detailed Technical Specification
LAPS tool requirement
- Active Directory: Windows Server 2003 Service Pack 1 (SP1) or later
- Managed domain members: Windows Server 2003 SP2 x86 or x64 later
- Management tools requirement: .NET Framework 4.0, Windows PowerShell 2.0 or later, Group Policy Management Console, Active Directory Domain Services management tools
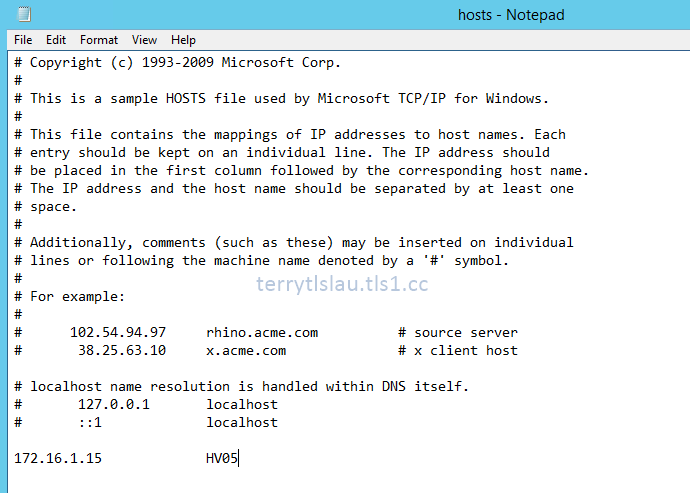
Lab environment
- 1 x Domain Controller named DC01 is installed Windows Server 2012 R2
- 1 x Windows Server 2012 R2 member server named MS01 to install LAPS
- 2 x domain workstations are installed Windows 7 and 8.1 named W7 and W8.
Prerequisites
Download and save LAPS installation files on C:\Temp of MS01 from the following web site. Local Administrator Password Solution (LAPS)
Make sure the configuration account is a member of Schema Admins of your domain forest.
Install Group Policy Management Console and AD DS and AD LDS Tools on MS01.
Create a new OU named workstations and move W7 and W8 into this OU.
Create 2 domain user accounts R1 and R2 for testing.
Create a local user account named Nimda and add into local administrator group in Windows 7 and Windows 8.1
1. Log in MS01 as Domain Administrator.
2. Navigate to C:\Temp and then run LAPS.x64 to install LAPS with full installation.
4. Perform Import-Module AdmPwd.Ps to import the PowerShell module for LAPS.
10. Edit the GPO and then extend "Computer Configuration > Policies > Administrative Templates > LAPS".
Password Settings: Enabled
Password Complexity: Large letters + small letters + number + specials
Password Length: 16
Password Age (Days): 30
13. Double click Name of administrator account to manage and then select the following settings.
Name of administrator account to manage: Enabled
Administrator account name: <local administrator account name of computers>
14. Click OK.
15. Double click Do not allow password expiration time longer than required by policy and Enable local admin password management, and then select Enable.
At this moment, W7 and W8 have been installed LAPS. I will install LAPS on W7 to verify the result.
Retrieve Password
1. On W7, log in as Domain Administrator.
2. Run LAPS installation tool with typical installation.
msiexec /i LAPS.x64.msi or LAPS.x86 .msi /quiet
3. After installation, perform gpupdate /force to update the Group Policy.
4. Back to MS01, log in as R1.
5. Launch LAPS UI.
6. Under "ComputerName", enter W7 and then click Search.
7. Under "ComputerName", enter W8 and then click Search.
8. On MS01, log in as R2.
9. Launch LAPS UI.
10. Under "ComputerName", enter W7 and then click Search.
Remark: We can perform Get-AdmPwdPassword -ComputerName <computername> to get the local administrator password by PowerShell.
Reset Password
1. On MS01, log in as R1.
2. Launch LAPS UI.
3. Under "ComputerName", enter W7 and then click Search.
4. Change "New expiration time" to next day and then click Set.
5. On MS01, log in as Domain Administrator.
6. Launch LAPS UI.
7. Under "ComputerName", enter W7 and then click Search.
8. Change "New expiration time" to next day and then click Set.
9. To grant R1 to reset local administrator password, we can perform Set-AdmPwdResetPasswordPermission -OrgUnit Workstations -AllowedPrincipals R1
Microsoft Security Advisory 3062591
Local Administrator Password Management Detailed Technical Specification
This posting is provided “AS IS” with no warranties, and confers no rights!